Test Servers for Heartbleed Vulnerability With This Handy Browser Tool
When you're done, we have this nice paper bag for you to breathe into.
Heartbleed is freaking everybody on the Internet out right now, specifically because as we’ve learned, it’s actually much more complicated than changing your passwords and hoping for the best. If you log in to a server while that server is still vulnerable, you might still be at risk, so you have to make sure that the site is no longer affected.
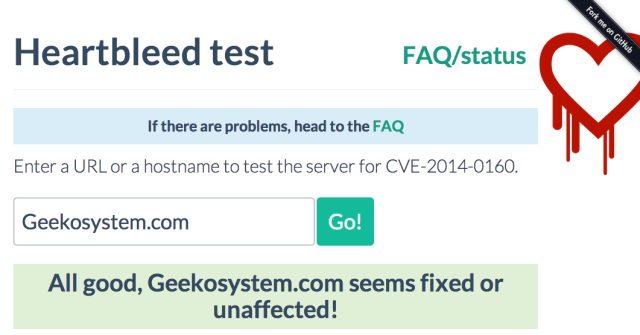
Mashable already has a good long list of sites that it’s safe to change your passwords for, but if you’re worried about an unnamed site that could possibly still be vulnerable, then use this tool by freelance cryptographer Filippo Valsorda. All you have to do is type in the domain for the site, and it tells you whether or not a website is currently being affected by the CVE-2014-0160 bug.
However, the tool can’t tell you if the website ever was vulnerable. As Valsora explains:
Unfortunately, there is no real way to check if a certificate have been re-keyed (a certificate can be re-keyed without dates being updated, and many CAs are doing this).
Moreover, the security risk of a patched server with a old cert is way lower, an attacker would need to be intercepting your traffic to take advantage of this. So I feel that the priority now is getting users to change passwords that might have been leaked to the world, not to a really skilled roommate, their malicious ISP or the NSA (these 3 being the few that can probably MiTM you).
He recommends that it’s the responsibility of the site owners to inform their users of possible vulnerabilities, and that they should “invalidate all users passwords and ask for them to be reset via email on first login.”
If you’re having problems with the tool, head to the FAQ or to Valsora‘s Twitter page to check out the known issues.
(Via Daveio, image via Flippo.io)
- Minecraft’s servers were apparently affected
- A five-year-old discovered an Xbox account security hole
- Pinterest recently hacked and invaded by butts
Have a tip we should know? [email protected]