Major Twitter Security Flaw Exploits Mouseovers (Update: Twitter Reports Patched)

If you arrived here from Twitter.com today, you should close that window ASAP; if your stream of tweets has been looking strange and full of code today, this is why. A major security flaw on Twitter.com has been exposed which allows users to exploit the onMouseOver Javascript command to cause other users to trigger pop-up messages or redirects to third-party websites merely by rolling over a Tweet with their cursors.
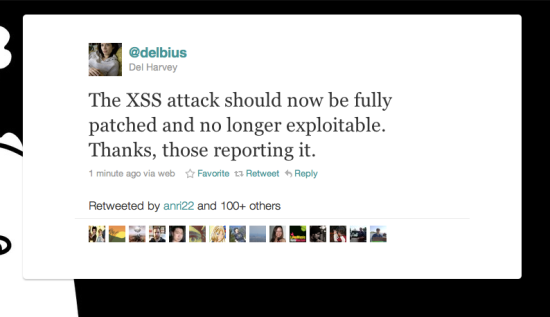
Update3: Twitter reports that the XSS vulnerability has been patched.
Update: It’s worse now: Reports are surfacing that code can be activated without even a mouseover, so avoid Twitter.com entirely for the time being.
Web security firm Sophos reports:
It looks like many users are currently using the flaw for fun and games, but there is obviously the potential for cybercriminals to redirect users to third-party websites containing malicious code, or for spam advertising pop-ups to be displayed.
Hopefully Twitter will shut down this loophole as soon as possible – disallowing users to post the onMouseOver JavaScript code, and protecting users whose browsing may be at risk.
Some users are also seemingly deliberately exploiting the loophole to create tweets that contain blocks of colour (known as “rainbow tweets”). Because these messages can hide their true content they might prove too hard for some users to resist clicking on them.
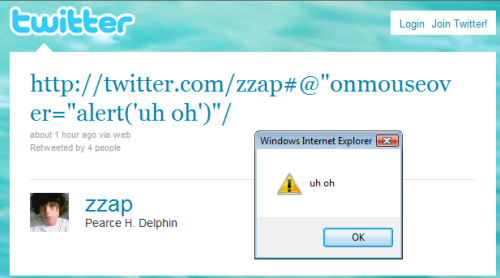
Update: More background on the flaw: Apparently, it was discovered by an Australian teenager going by the handle “zzap.”

Netcraft informs us that it took less than two hours for hackers to discover and implement the flaw on a wide scale, and that one of its first uses was (what else) people mouseover Rickrolling each other:
zzap (jokingly?) suggested that nobody should tell the 4chan forum about the XSS vulnerability; however, some other users have already started Rickrolling other users by tweeting Rick Astley lyrics in pop-up JavaScript alert messages. It is feasible for much larger JavaScript payloads to be loaded from external websites, which could allow complex cross-site request forgery attacks (CSRF) against authenticated Twitter users.
…
Rather impressively (and also unfortunately), it took less than 2 hours for hackers to exploit this vulnerability in a wide scale fashion. Many users have already been targeted by scripts which attempt to propagate in a worm-like fashion, or load larger JavaScript payloads from external locations.
Also, as more technical details about the hack emerge, it appears that Twitter’s t.co URL shortener is partly to blame. t.co renders the HTML for URLs that follow; TNW reports that hackers have discovered that they can abuse t.co by closing the href attribute early.
http://t.co/@“onmouseover=”etc”/ would render as <a href=”http://t.co/@” onmouseover=”etc”>http://t.co/@“onmouseover=”etc”/</a>. That first double quote in the malicious URL closes the href attribute and allows for javascript events to be included afterwards.
Third-party Twitter clients like Tweetdeck are unaffected by the onMouseOver flaw, however, so at present, they’re the safest way to navigate Twitter until the company fixes the bug.
(Sophos via TNW; Netcraft; pic via Mashable)
Have a tip we should know? [email protected]